The Complete API Security Stack for 2026: 73% of Data Breaches Start With Compromised APIs
Zero Trust Architecture + OAuth 2.0 + APIOps: The Three-Layer Defense Every Enterprise Needs
Your API security stack is the difference between a secure enterprise and tomorrow’s breach headline. APIs now account for 71% of all web traffic and 17% of all reported security vulnerabilities. Wallarm’s 2026 API ThreatStats Report reveals that 43% of actively exploited vulnerabilities tracked by CISA are API-related. Traceable AI’s research found that 57% of organizations suffered API-related breaches in the past two years, with 74% reporting multiple incidents. And 84% of security professionals reported experiencing at least one API security incident in the past 12 months.
The attack surface isn’t shrinking — it’s exploding. AI agents built on Claude Code, Codex, and other tools are generating millions of new API endpoints. The Model Context Protocol (MCP) alone accounted for 315 vulnerabilities in 2025 — growing 270% in a single quarter. When an MCP server gets compromised, attackers don’t just access data — they gain control over autonomous AI workflows.
This guide covers the complete API security stack for 2026: the three-layer defense (Zero Trust + OAuth 2.0 + APIOps) that protects your APIs from the endpoint level to the operational level, with actionable implementation steps your team can deploy this quarter.
Why APIs Are Now the #1 Enterprise Attack Surface?
| Metric | Data Point | Source |
|---|---|---|
| API-related vulnerabilities (2025) | 11,053 of 67,058 (17%) | Wallarm 2026 ThreatStats |
| CISA exploited vulnerabilities that are API-related | 43% | Wallarm / CISA KEV Catalog |
| Organizations with API breaches (past 2 years) | 57% | Traceable AI 2025 Report |
| Organizations with multiple API breaches | 74% | Infosecurity Magazine |
| Security professionals reporting API incidents | 84% | Frontegg/Industry surveys |
| Organizations with API security issues (12 months) | 99% | CybelAngel Q1 2025 |
| Organizations can detect API attacks | Only 21% | Traceable AI |
| Organizations can prevent 50%+ of API attacks | Only 13% | Traceable AI |
| AI + API vulnerability overlap growth (YoY) | 79% increase | Wallarm |
| API-related AI threats (YoY growth) | ~400% (439 → 2,185) | Wallarm |
Layer 1: Zero Trust Architecture Trust Nothing, Verify Everything
Zero Trust is the basis of modern API security because the old perimeter, based model no longer works. When APIs are accessed by employees, contractors, partners, mobile apps, third-party integrations, and autonomous AI agents, your network no longer has an “inside” and “outside“. Every request has to prove that it is legitimate.
Core Zero Trust principles for APIs:
a. Verify every request
Authenticate and authorize every API call before processing it. A certain internal service cannot be exempted from such treatment, and there must not be any implicit trust for a request originating from the corporate network. The Salesloft/Drift OAuth breach in Q3 2025 compromised the APIs of Salesforce in multiple enterprises, including Cloudflare, Zscaler, Palo Alto Networks, and Google, by using stolen tokens to access these APIs. A single exploited trust boundary cascaded across the whole partner ecosystem.
b. Least privilege access
Employ the principle of least privilege access. Provide each API consumer only the minimum necessary permissions. Implementation of Role-Based Access Control (RBAC) can be used for broad permissions, whereas Attribute, Based Access Control (ABAC) can be used for more granular, context-aware decisions. Every API key, every service account, and every user token should be limited to the minimum necessary access.
c. Micro-segmentation
Split up your API setup into separate parts, each having its own access rules. If a hacker gets into one API spot, micro-segmentation stops them from spreading to other things. This is super important when you have AI helpers that might get into different internal systems through MCP servers.
d. Continuous monitoring
Zero Trust isn’t something you do once and forget – it’s about always checking. Watch every API thing that happens for weird stuff, odd access, and when rules are broken, all in real-time. Track how long it takes to spot (MTTD) and fix (MTTR) every API security problem.
e. Implementation checklist
How to do it: Use an API gateway as the main control spot. Use mutual TLS (mTLS) for all the talk between services. Make sure everyone is who they say they are on every request with your IAM setup. Split up the network with different access rules for each API group. Use behavioral analytics to spot weird stuff as it happens. Make sure policies are automatically enforced to stop fishy request before they hit the backend stuff.
Layer 2: OAuth 2.0 The Authentication Standard That Actually Works
OAuth 2.0 continues to be the predominant standard for API authentication in 2026. The main reason is that it addresses the primary issue: how to grant access in a controlled manner without revealing the credentials of the user. For example, if a fintech partner wants to get transaction history, OAuth will help you give the partner the limited access they need to do their work, and at the same time, it enables you to keep the customer’s username and password a secret.
Here is why OAuth 2.0 is more significant than ever in 2026:
AI agents are presenting a new hurdle for authentication. Every time Claude Code is allowed to access your GitHub repositories, when an MCP server is permitted to connect to your internal databases, or when an AI workflow is authorized to make API calls across various serviceseach case requires delegated, limited access that OAuth 2.0 was conceived to offer. With the skyrocketing number of agent to API interactions, OAuth is becoming the authentication layer that prevents AI-enabled automation from turning into AI-enabled breach vectors.
The OAuth 2.0 + JWT stack:
| Component | Function | Why It Matters |
|---|---|---|
| OAuth 2.0 | Delegated access framework | Grants limited permissions without credential sharing |
| JWT (JSON Web Tokens) | Token format | Stateless, verifiable, includes claims and expiry |
| OpenID Connect (OIDC) | Identity layer on top of OAuth | Verifies user identity, not just authorization |
| PKCE (Proof Key for Code Exchange) | Protection for public clients | Prevents authorization code interception |
| Mutual TLS (mTLS) | Certificate-based auth | Both client and server verify each other |
| Token rotation | Regular credential refresh | Limits the damage window if tokens are stolen |
Critical implementation rules:
- Never resort to using API keys for verifying the identity of users. API keys are designed to identify applications, not users. They do not come with user context and, therefore, should not be used as a substitute for OAuth in systems that are public-facing. Only use API keys for server, to, server interaction within trusted environments, and make sure they are accompanied by further security measures.
- Make sure to have token expiration and rotation in place. Short-lived access tokens (15 to 60 minutes), along with refresh tokens, basically limit the time window that damage can be inflicted if a token is somehow stolen. The Salesloft breach was partly successful because the stolen OAuth tokens were still valid long enough to be exploited across multiple enterprises.
- Go for the least privilege model. Each OAuth token must explicitly state the kind of resources it can interact with. In other words, a token that is simply granted access to read user profiles should never be able to write to payment APIs. Always aim to grant your tokens the minimum set of permissions required for a specific operation.
- All public clients should be using PKCE. Phone apps, single-page web apps, or any other client applications lacking the capability to securely store the client secret must implement PKCE in order to ward off authorization code interception attacks.
Layer 3: APIOps Security as Code, Not Security as Checklist
APIOps applies DevOps principles to API management, treating API security policies, configurations, and governance as code that is versioned, tested, deployed, and monitored through CI/CD pipelines. This is the point where most enterprises fail: they correctly implement Zero Trust and OAuth, then allow governance to deteriorate because it relies on manual processes.
Why APIOps is the layer most organizations miss:
Only 14% of organizations currently have an API posture governance strategy in place (Salt Security data). That means 86% are managing API security through ad hoc processes, manual reviews, and hope.
Developers push new API endpoints every sprint in an environment like this, so manual governance can’t keep up. A security review can misconfigured endpoint only when it is detected, and such an endpoint could have been live for weeks without a problem.
The APIOps Framework:
- Policy, as code. Make a policy for every security measure, authentication requirements, rate limits, input validation rules, and access controls that are coded and live in your repository alongside your API definitions. When policies are code, they’re version, controlled, peer, peer-reviewed, and automatically enforced.
- Automated security testing in CI/CD. Automated security checks should be triggered automatically with every API deployment: schema validation, authentication verification, input fuzzing, and authorization boundary testing.
- No deployment that fails security tests will ever be released to production. End of story. API discovery and inventory management. It’s impossible to protect something you haven’t identified.
- Use continuous API discovery to find shadow APIs, zombie APIs (deprecated but still receiving traffic), and undocumented endpoints. API sprawl prevention is the #1 API security challenge, according to 48% of organizations.
- API discovery and inventory management. Knowing what you have is the first step in securing it. Make a habit of regular API discovery, which will help you find shadow APIs, zombie APIs (those that are deprecated but still getting traffic), and unauthorised endpoints. Stopping API sprawl has been recognized as the single biggest challenge to API security by 48% of the organizations surveyed.
- Runtime protection and monitoring. Put into use runtime monitoring that can spot an attack as it is happening, not after the attacker has already gotten in. Among all API attack methods, DDoS attacks are the leading cause of breaches (38% of incidents), followed by fraud (29%) and the exploitation of known vulnerabilities (29%). Real-time rate limiting, behavioral analytics, and automated blocking are effective measures for preventing these attacks from causing any damage.
- Continuous compliance mapping. Automatically map each API security measure to the regulatory requirements relevant to your organisation (GDPR, HIPAA, PCI, DSS, SOC 2). When auditors come asking for proof, draw it from your policy, as a code repository, not from a pile of manually created documentation.
The Three-Layer Stack in Action: How It Works Together
| Attack Scenario | Layer 1: Zero Trust | Layer 2: OAuth 2.0 | Layer 3: APIOps |
|---|---|---|---|
| Stolen API credentials | Continuous verification detects anomalous behavior | Short-lived tokens limit the damage window | Automated alerts trigger incident response |
| Unauthorized data access | Least privilege prevents access beyond scope | Scoped tokens are restricted to specific resources | Policy-as-code enforces access controls |
| DDoS attack on the API | Micro-segmentation contains a blast radius | Rate limiting per token/client | Automated scaling + real-time blocking |
| Compromised AI agent (MCP) | Zero Trust blocks unauthorized lateral movement | OAuth scopes limit agent permissions | Runtime monitoring detects abnormal agent behavior |
| Shadow/zombie API exploit | Network segmentation limits exposure | No valid tokens for unmanaged APIs | Continuous discovery identifies unknown endpoints |
| Supply chain API attack | Verify every partner API request | Partner-specific scoped tokens | Automated testing of partner API connections |
How to whip Your APIs Into Shape: A 6-Step Plan?
- Step 1: Inventory Time (Weeks 1-2) – First off, you need to know what APIs you even have. Hunt them down, maybe with tools. Look for those sneaky APIs, the ones without docs, and those ancient services that are still somehow kicking. Gotta know what you’ve got before you can defend it, right?
- Step 2: API Gateway to the Rescue (Weeks 2-4) – Next, drop in an API gateway right in the center for good measure. It’s your bouncer. Make all API traffic go through this thing. That way, you’ve got the same rules for logging in, permissions, speed, and keeping watch for suspicious people.
- Step 3: Get with OAuth 2.0 + Zero Trust (Month 1-2) – Time to lose the basic logins. Switch over to OAuth 2.0 and JWT tokens, which are much safer and more reliable. Services should use mutual TLS when chatting with each other. Give everyone the bare minimum access they require and cut things up into safe zones. Double-check who people are all the time.
- Step 4: APIOps to the Rescue (Month 2-3) – Turn those security rules into actual code. Toss some auto security tests into your building and deployment. Never stop searching your systems for listing APIs on the go. Use runtime monitoring to get the alarm. The world is waiting for you.
- Step 5: Lock Down Your AI Buddies (Month 3-4) – Don’t forget security for your AI agents, MCP servers, and all those automated processes. Use Zero Trust for every single chat between your agents and an API. Give AI services the fewest OAuth permissions possible. Watch how those agents behave and look for anything fishy.
- Step 6: Always Getting Better (Always) – Keep looking at your security rules, and tweak them every three months. Do regular security tests on your API endpoints. See how fast you can find and fix stuff, and how often you get fake alarms. Make sure your controls match the rules you need to follow, and make those audit reports happen by themselves.
Mistakes That Cause API Breaches
- Thinking API Security is a One-Time Thing: API security never stops. You’re always adding stuff – new endpoints every sprint, new integrations monthly, and AI agents quarterly. Security has to keep up. Companies that think they can just set up API security once are the ones getting hacked.
- Only Protecting REST APIs: These days, companies use all sorts of APIs: REST, GraphQL, WebSocket, gRPC, Kafka, and MQTT. Your security should cover everything, not just REST. People are hitting event-driven APIs (like Kafka and WebSocket) harder now, probably because they’re not as secure as REST.
- Not Seeing What Third-Party APIs Are Doing: Attacks through supply chain APIs are on the rise. Remember the Salesloft/Drift thing in Q3 2025? It went through Salesforce APIs and messed up Cloudflare, Zscaler, Palo Alto Networks, and Google. Every API connection from someone else is a possible way in. Watch those partner APIs and lock them down just like you would your own stuff.
- Forgetting About AI Agent API Stuff: AI agents calling APIs means way more requests and a bigger risk if something goes wrong. MCP vulnerabilities jumped like crazy last quarter. If you’re using AI agents, you need to make sure agent-to-API traffic is secure.
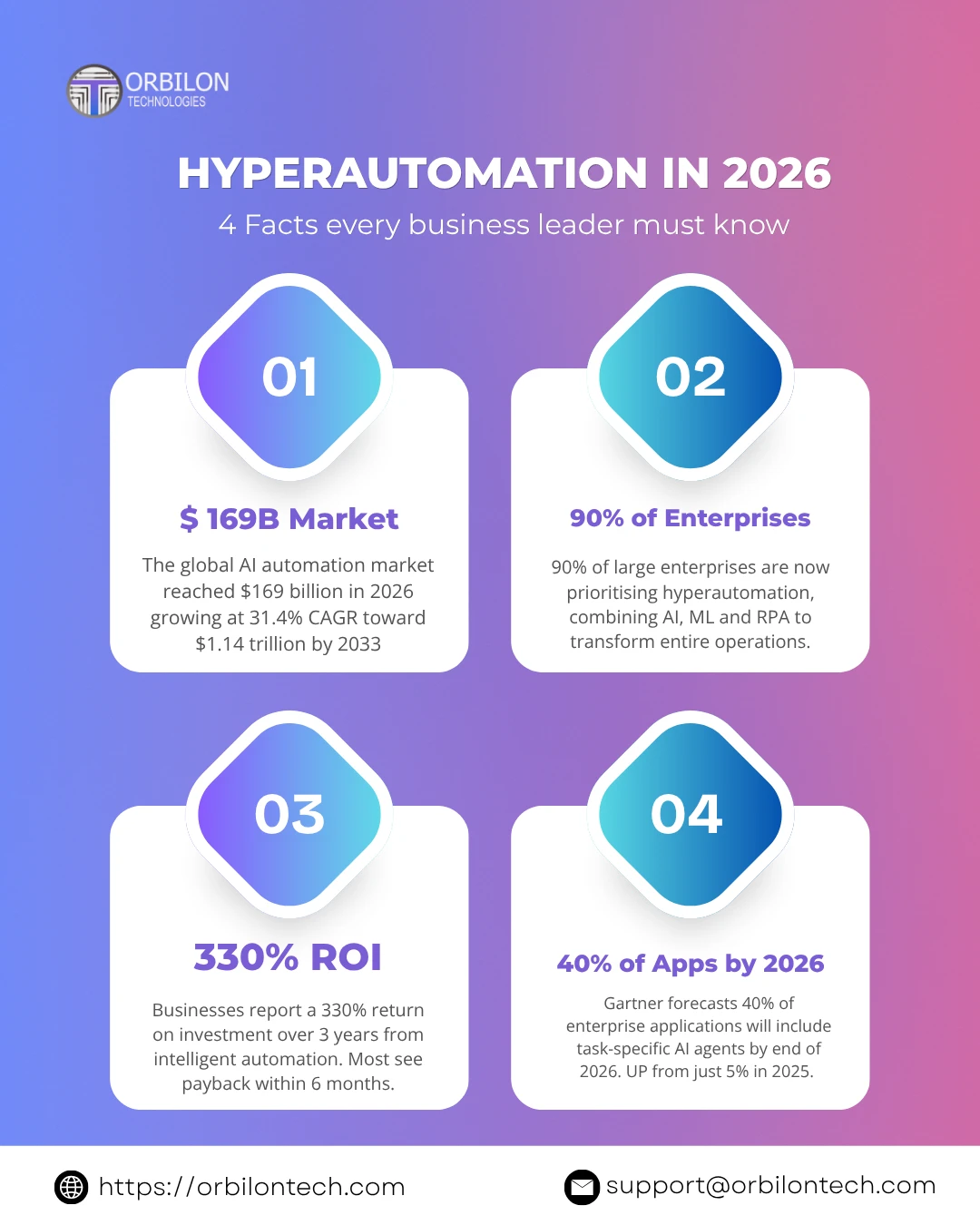
Want to Protect Your APIs?
At Orbilon Technologies, we assist businesses with checking, building, and putting in place total API security—from Zero Trust setup and OAuth 2.0 to APIOps and AI agent security. We create a defense that makes your APIs a plus, not a problem.
We’ve seen some good results: revenue up 97%, handle time improved by 42%, and costs down 20-30% in just 90 days.
- Rated 4.96 on Clutch
- Website: orbilontech.com
- Email: support@orbilontech.com
APIs are the starting point for 73% of breaches. Get your defense going now.
Want to Hire Us?
Are you ready to turn your ideas into a reality? Hire Orbilon Technologies today and start working right away with qualified resources. We will take care of everything from design, development, security, quality assurance, and deployment. We are just a click away.