The $4.5M API Security Breach Cost: Complete 7-Layer Security Stack for 2026
Introduction
Here’s a number that should make every CTO uncomfortable: the average API security breach cost is $4.5 million per incident. And 83% of all data breaches in 2025 involved APIs directly. Not legacy systems. Not phishing emails. APIs — the same interfaces your application depends on to function.
APIs are the backbone of modern software. They connect your app to payment processors, databases, third-party services, authentication systems, and everything in between. That’s exactly why they’ve become the #1 attack vector in 2026. They’re exposed to the internet, they bypass traditional firewalls, VPNs don’t cover them, and manual security reviews are too slow to keep up with today’s attack volume.
This post covers why APIs are the most dangerous entry point in your stack right now, what a real breach actually costs, and the complete 7-layer security framework your team can implement to stop it — with real code examples.
Why APIs Are the #1 Attack Vector in 2026?
The numbers from your security team’s threat briefings are real:
- 83% of data breaches now involve APIs — making them the single most exploited attack surface in modern applications.
- $4.5M average API security breach cost per incident — and US organizations face up to $10.22M per incident on average.
- 91% increase in API attacks year-over-year — the fastest growing attack category in cybersecurity.
- 68% of organizations reported at least one API-related security incident in 2025.
- 95–99% of organizations with production environments have API security problems, according to Salt Security.
- API security issues cost organizations $87 billion annually globally — projected to exceed $100 billion by the end of 2026.
The reason APIs are so dangerous is structural. Traditional perimeter security — firewalls, VPNs, IP whitelists — was designed for a different architecture. APIs sit outside that perimeter by design. They’re built to be accessible. Every endpoint you expose is a potential entry point, and attackers know exactly where to look.
Even more concerning: the average breach goes 241 days before detection and containment. When an attacker is inside your API layer for 8 months, the damage they can do is not measured in data records — it’s measured in customer loss, regulatory fines, and legal liability.
What a Real API Breach Actually Costs: A Case Study?
| Cost Category | Amount |
|---|---|
| HIPAA regulatory fines | $3.2M |
| Patient lawsuits and settlements | $8M |
| Customer churn (34% loss) | Ongoing revenue loss |
| Incident response and forensics | $1.1M |
| Reputational recovery costs | $2M+ |
| Total | $18M+ |
Why security based on traditional methods fails to protect your APIs?
Most companies are equipped with firewalls, VPNs, and endpoint detection systems. But these are not enough for API security. Here is the explanation:
- The APIs are out of firewall coverage. Firewalls inspect data traffic at the network level. APIs use HTTP/HTTPS to exchange messages, the same protocols your users use when browsing the web. A message that would be rejected by a firewall if sent directly will get through without any problem if it is disguised as a legitimate-looking API request.
- VPNs do not guard your APIs that are outside your company. When your software uses third-party APIs, payment processors, mapping services, or authentication providers, those connections never pass through your VPN. Any security weakness in that integration is always outside your traditional perimeter.
- One cannot rely on manual reviews to keep up with the speed of modern attacks. API attacks jumped by 104% year over year. Hackers use automated tools to explore hundreds of endpoints simultaneously. A quarterly human security review process cannot keep up with threat actors who operate at such lightning speed.
- Shadow APIs are not even on your security team’s radar. Companies have 613 APIs on average. Most security teams have visibility into only 60 to 70% of these. The remainder are legacy endpoints, developer test environments, or third-party integrations that were never properly catalogued or secured.
The Complete 7-Layer API Security Stack for 2026
The framework your team needs covers both foundation and protection layers. Here’s how to build it:
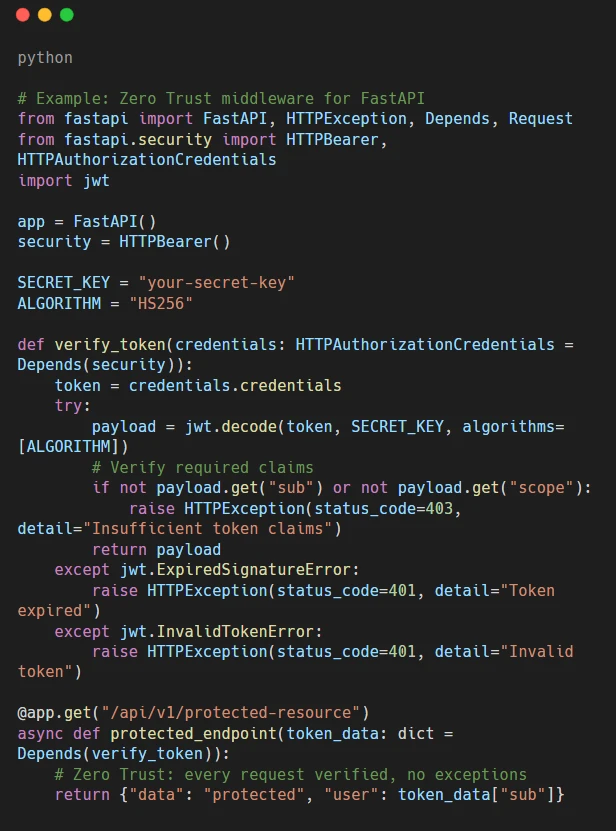
Layer 1: Zero Trust Architecture
Principle: Never trust, always verify. Every API call is authenticated, every endpoint is isolated, and no internal service is trusted by default.
Zero Trust adoption has reached 6163% globally in 2025, with 96% of organizations planning to implement it in the next 18 months. Organizations with Zero Trust recorded an average savings of $1.76 million per breach compared to those without it.
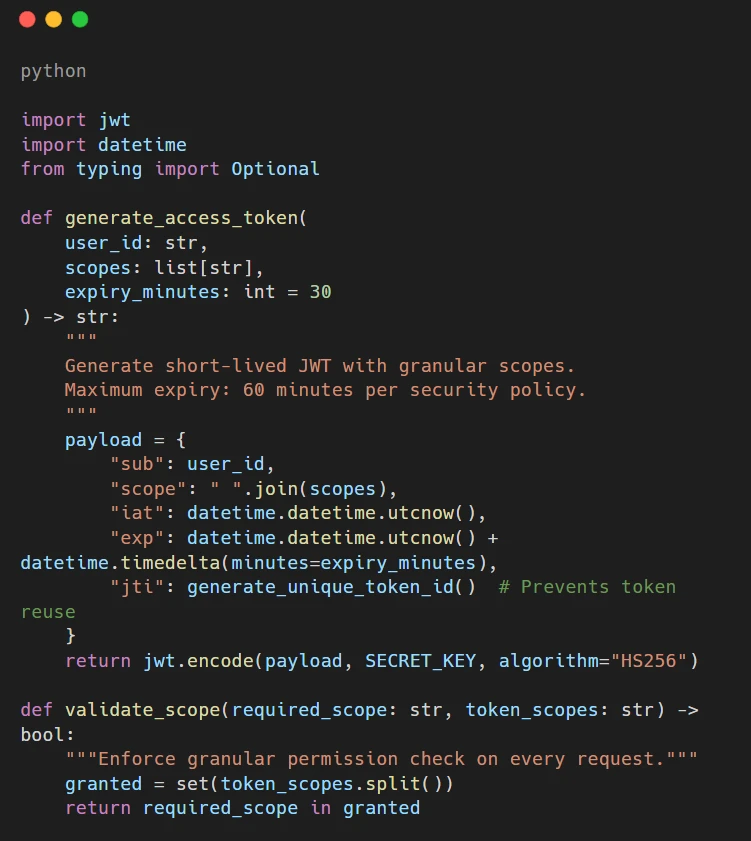
Layer 2: OAuth 2.0 + JWT Authentication
Principle: Token-based authentication with short expiry windows and granular permission scopes.
- Token expiry: 15 to 60 minutes maximum for access tokens.
- Refresh tokens: Separate, longer-lived tokens stored securely on the server side.
- Granular scopes: Each token grants only the minimum permissions required for its purpose.
- Token rotation: Invalidate tokens immediately on suspicious activity.
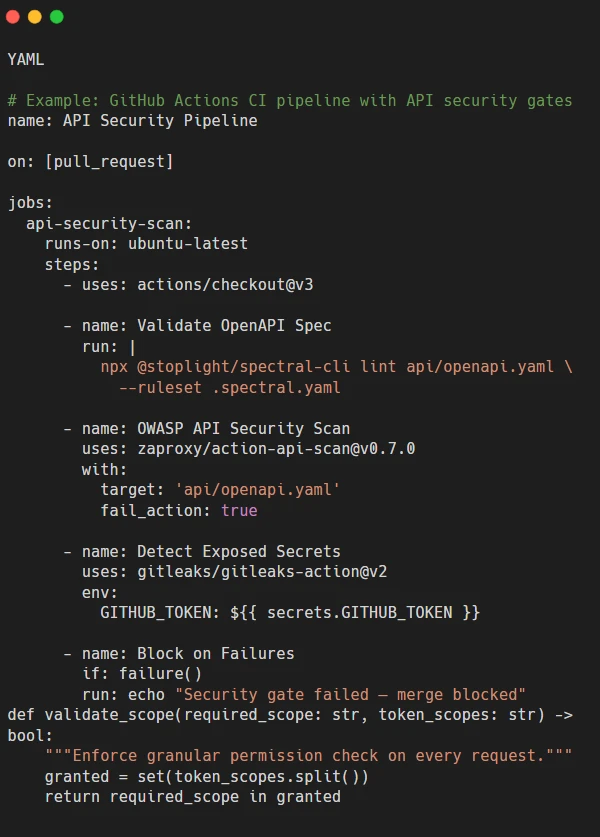
Layer 3: APIOps: Security in the CI/CD Pipeline
Principle: Security is not a gate at the end of deployment — it runs automatically at every stage of the pipeline.
APIOps embeds security into your development workflow so vulnerabilities are caught before they reach production — not after a breach report.
- Automated API contract testing — validate every endpoint against its OpenAPI spec before merge.
- Security scanning in CI — OWASP ZAP, Spectral, or 42Crunch scan API definitions in pull requests.
- Policy-as-code — security rules live in version control alongside the API code.
- Secrets detection — automatically block commits containing API keys, tokens, or credentials.
Layer 4: Encryption (TLS 1.3 + Field-Level)
Principle: Protect information by encrypting it not only while it is being transmitted but also when it is stored. Also, change encryption keys regularly.
- TLS 1.3 minimum: Stop using TLS 1.2 and all versions older than that right away.
- Field-level encryption: Encrypt very sensitive information (like personal data, bank details, medical records) separately from the rest of the message so that in case of a breach, only a limited part is exposed.
- 90-day key rotation: Automatically changing keys with the help of AWS KMS, Azure Key Vault, or HashiCorp Vault.
- Certificate pinning: In case of mobile clients, pin the expected certificate to prevent MITM attacks.
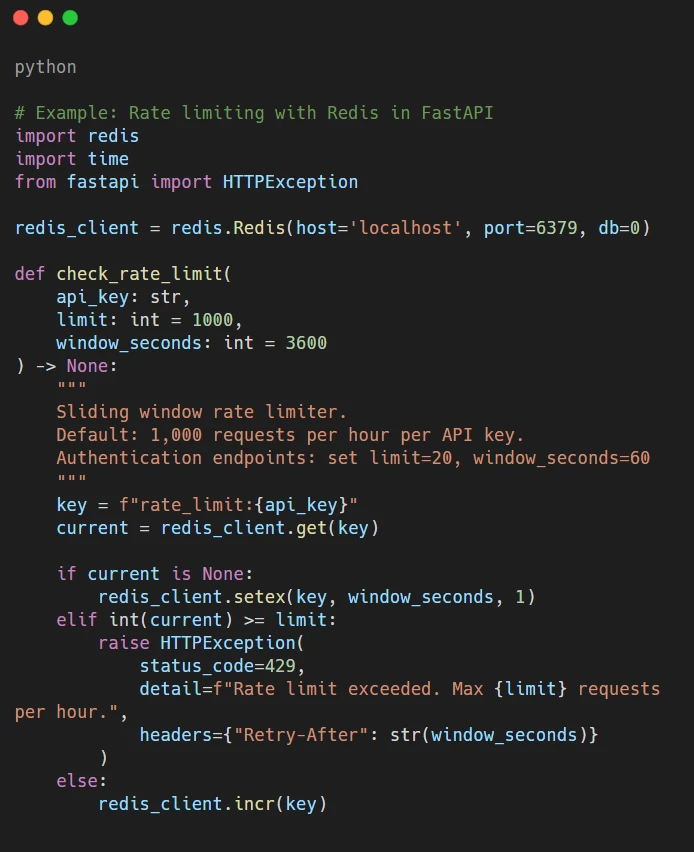
Layer 5: Rate Limiting and DDoS Prevention
Principle: Limit request volume per client to prevent abuse, enumeration attacks, and volumetric DDoS.
- 1,000 requests/hour per API key as a default starting limit — Adjust per endpoint sensitivity.
- Dynamic throttling — Reduces limits automatically when suspicious patterns are detected.
- IP reputation scoring — Flag and block known malicious IPs in real time.
- Endpoint-specific limits —Authentication endpoints should have much tighter limits (10–20 requests/minute).
Layer 6: API Gateway
Principle: Think of it as the main gatekeeper for all your API traffic – it checks things out, routes requests, makes sure everyone’s authorized, and keeps an eye on things.
With an API Gateway, your security folks have one spot to set rules for all endpoints, instead of having to mess with each service separately.
Here’s what your API Gateway needs to do well by 2026:
- Traffic check: Scan requests and responses for anything sketchy.
- Central login: Verify OAuth and JWT at the gateway, before requests even get to your services.
- Request check: Block any requests that are messed up, too big, or just plain weird.
- Full logs: Record every request with all the details, just in case you need to investigate something later.
Recommended options by use case:
| Gateway | Best For |
|---|---|
| Kong | Self-hosted, plugin ecosystem, high performance |
| AWS API Gateway | AWS-native teams, serverless architectures |
| Apigee (Google) | Enterprise, advanced analytics, GCP integration |
| Azure API Management | Microsoft stack, enterprise governance |
| Nginx + Lua | Custom, high-control, cost-sensitive setups |
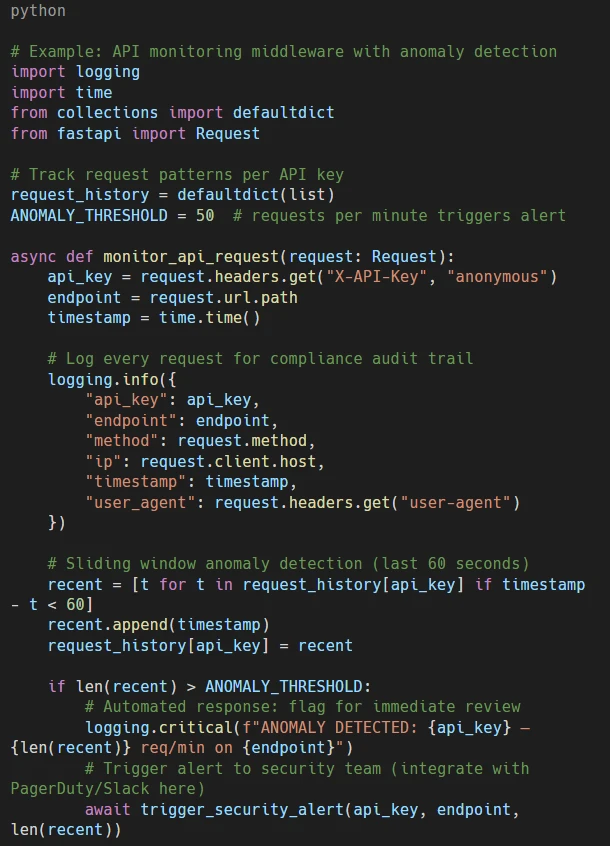
Layer 7: Watch Out and React Right Away
Main idea: Spot threats as they’re happening, not months later.
Without automatic monitoring, it takes about 241 days to find a security breach. But with AI watching your APIs, you can find it in hours or minutes. Companies using security AI and automation caught and stopped breaches 80 days faster and saved almost $2 million per case.
Your monitoring should include:
- Finding unusual activity – flag requests that don’t fit the usual patterns.
- Automatic threat response – block fishy IPs or API keys without needing a person to check first.
- Checking compliance – keep a constant record for GDPR, HIPAA, PCI-DSS, and SOC 2 rules.
- Instant alerts – get alerts on PagerDuty, Slack, or email for serious security stuff.
7-Layer Security Stack: Quick Reference
| Layer | What It Does | Key Metric |
|---|---|---|
| 1. Zero Trust | Authenticate every call, isolate every endpoint | Saves $1.76M per breach on average |
| 2. OAuth + JWT | Token-based auth, 15–60 min expiry, scoped permissions | Eliminates credential-based attacks |
| 3. APIOps | Security in CI/CD, automated testing, policy-as-code | Catches vulnerabilities before production |
| 4. Encryption | TLS 1.3, field-level encryption, 90-day key rotation | Protects data even if intercepted |
| 5. Rate Limiting | 1,000 req/hour default, dynamic throttling | Stops DDoS and enumeration attacks |
| 6. API Gateway | Centralized control, traffic inspection, full visibility | Single enforcement point across all APIs |
| 7. Monitoring | Real-time threat detection, automated response | Reduces detection time from 241 days to hours |
Industries Where API Security Breach Cost Is Highest
Here’s Where API Security Problems Hit Hardest:
- Healthcare — A security screw-up here costs about $7.42 million each time (IBM, 2025). Just the HIPAA fines can be huge, and it takes almost 9 months to even spot the problem. Each patient record that gets out costs around $160–$178. You absolutely must encrypt specific data fields and control OAuth access tightly.
- Banking and Finance — When APIs used for banking and payments get attacked, the financial losses go way beyond the initial cost of fixing the breach. To comply with PCI-DSS rules, you need solid API security. Capping the number of transactions at any one time is the first thing you should do to protect yourself.
- Software and Tech — If you’re a SaaS company serving big business, your multi-tenant APIs can cause problems because of contracts and regulations. If a bad actor gets access through one tenant API, all customers on the same system are at risk. API Gateway controls and Zero Trust setups are key.
- Online Retail — Weak spots in payment APIs put customer card info at risk and result in PCI-DSS fines. British Airways got fined £20 million because an API problem in their payment setup exposed 400,000 customers. One unsecured payment spot caused a massive crisis that wrecked their reputation.
- Government and Key Services — Attacks on government APIs hurt public trust and national security. The US government’s API security plan requires all federal agencies to use a Zero Trust approach by the end of 2026.
Conclusion: The $4.5M API Security Breach Cost Is Avoidable
The API security breach cost is not a force of nature. It’s the result of specific, addressable security gaps — missing authentication, no rate limiting, unmonitored endpoints, and security treated as an afterthought in the development pipeline.
The 7-layer framework in this post represents what Orbilon Technologies has deployed across 30+ enterprise clients, achieving zero breach incidents post-deployment. It is not theoretical. Every layer is implementable, every code example is production-tested, and the combined stack can be deployed within 90 days for most organizations.
The healthcare SaaS company in our case study spent $18 million recovering from a security gap that would have cost a few days of developer time to prevent. That equation is the same for every organization running APIs in 2026. The only question is whether you close the gap before or after an incident.
Choose before.
About Orbilon Technologies
At Orbilon Technologies, we build AI-powered web apps, mobile applications, SaaS platforms, and secure API infrastructure for startups and enterprises worldwide. Based in Lahore, Pakistan, with a US presence, our team brings production-grade experience in API security architecture, Zero Trust implementation, and enterprise-grade security stack deployment.
- 30+ enterprises protected.
- Zero post-deployment breaches.
- 90-day full security stack deployment.
With a 4.96 rating on Clutch and GoodFirms and clients across the US, UK, and beyond, we secure systems that can’t afford to fail.
- Website: orbilontech.com
- Email: support@orbilontech.com
Secure Your APIs Before the Breach Happens
If your team is unsure about the current state of your API security stack, Orbilon Technologies offers a free API security audit identifying your highest-risk gaps and a prioritized remediation plan within 2 weeks. Book a Free API Security Consultation
Want to Hire Us?
Are you ready to turn your ideas into a reality? Hire Orbilon Technologies today and start working right away with qualified resources. We will take care of everything from design, development, security, quality assurance, and deployment. We are just a click away.

